Your Guide to AI in the GSOC
How security operations are benefiting from innovative tech (and how to get started in your program).
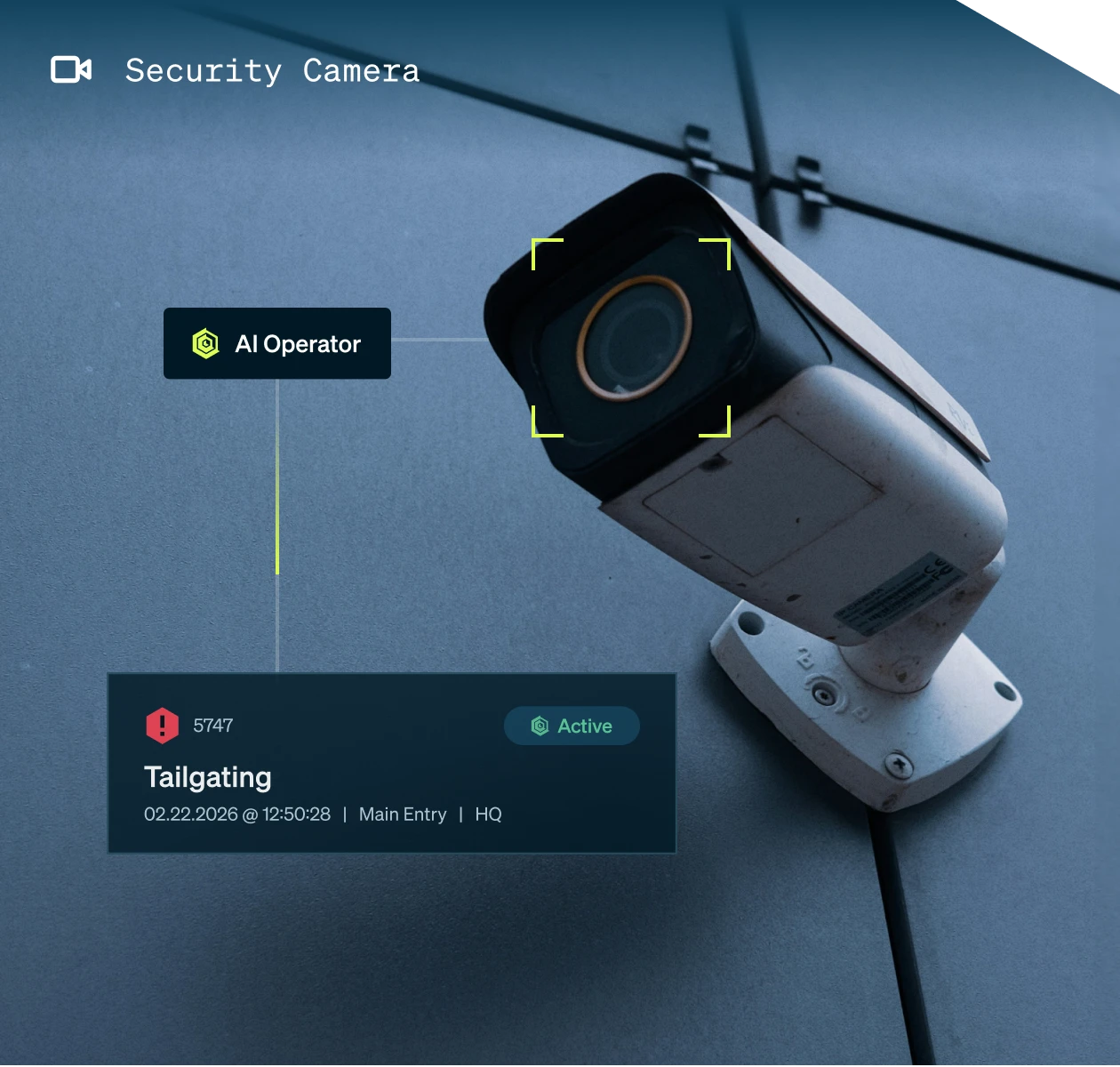
AI Operator processes every alarm so your team can focus on the ones that require a human decision.

Hundreds of camera alarms. Per day. Per site. And somewhere in that pile is a real threat.
Your operators are doing their best. But no human can reliably triage thousands of alarms a shift, distinguish a door propped open from a break-in, or stay sharp through hour four of false positives. The signal is in there. It’s just buried.
That’s not a people problem. That’s a system problem.
When everything looks urgent, nothing is. Operators burn through the noise and real threats slip by.
For a door that was left open. Again. Your security program loses credibility (and so do you).
Pattern analysis. Proactive threat identification. Strategic security oversight. It’s on the list. It never happens.

(3-step flow)
AI Operator receives the alert trigger and evaluates it instantly against other data feeds, your rules and configurations, taking into account your specific program and site context.
Routine event? Resolved automatically, with a full record of what happened and why. Genuine threat? Escalated to your operator queue immediately, with full context and suggested next steps according to your SOPs.
Operators see only what needs them. No noise. No second-guessing. Just real incidents, ready for human judgment.
AI Operator is configurable by camera, facility, floor, time of day, day of week, and alarm type. This isn’t black-box AI making decisions you can’t explain. You control exactly what gets automated: every AI Operator decision is based on your SOPs.
Start with one use case. Expand when you’re ready.
“For GSOC operators, noise reduction isn’t just a nice-to-have — it’s foundational. When operators aren’t buried in alerts they have to manually triage and dismiss, they can focus on what truly matters: proactive threat analysis, strategic decision-making, and protecting the organization at a higher level.”
91%
Alarms resolved without a human
40
Operator hours per week saved
Before any automation goes live, run a 30-day dry run. AI Operator works in shadow mode, evaluating your real alarm volume against your rules, and delivers a full report: what it would have resolved, at what accuracy, and what you would have saved.
You see the data before you make any decisions. That’s how we’d want it too.

The shift isn’t just operational. It’s cultural. When operators stop triaging false positives and start focusing on real threats, the whole security function moves forward.
Your team has time to address patterns. They surface emerging risks. They build the kind of proactive security program you’ve been trying to get to for years. And when the CFO asks what security delivered this quarter, you have an answer backed by data.


Let us show you what AI Operator would have handled last month — with your data, your alarm types, your sites.