Posted on March 20, 2026 by Andrew - Uncategorized
Overview
As security programs mature beyond gates, guards, and guns, leaders are turning toward technology to drive change. The biggest impact is happening in the security operations center, where traditional operational models are becoming unsustainable. This eBook breaks down how AI is transforming the GSOC — and gives you a practical starting point for your own program.
In this guide, we will:
- Explore how AI is being used to transform security operations – especially as resourcing becomes a challenge
- Provide practical insights for security professionals looking to effectively leverage AI tech across the enterprise
- Reveal real-world AI applications within a SOC environment to handle routine tasks and work alongside humans
Posted on March 20, 2026 by Andrew - Uncategorized
Overview
Build or outsource? It’s one of the most consequential decisions a security leader can make. This guide breaks down the trade-offs across cost, control, staffing, and technology — and gives you the right questions to make the call with confidence. There’s no universal answer. But there is a right answer for your organization.
This guide covers:
- The roles and functions of a global security operations center (GSOC)
- The differences between an in-house and outsourced GSOC (and what a hybrid model looks like)
- How to approach the decision to build a GSOC or outsource one
- Questions to ask GSOC-as-a-Service (GSOCaaS) vendors
- Sourcing components of an internal GSOC (and technology considerations to make during development)
Posted on March 9, 2026 by Andrew - Uncategorized
This eBook explores the biggest noise perpetrators in security operations centers and provides a step-by-step guide for building a strategy to address false alarms and other noise — before they burn out your operators.
Posted on March 9, 2026 by Andrew - Uncategorized

Growth shouldn’t break your security program. But for too many organizations, the systems that worked at 10 locations can’t hold up at 100. This guide walks security leaders through the core pillars of a scalable security architecture — from technology consolidation and GSOC structure to operator workflows and program measurement. Build a foundation that grows with your organization, not against it.
Posted on March 9, 2026 by Andrew - Uncategorized
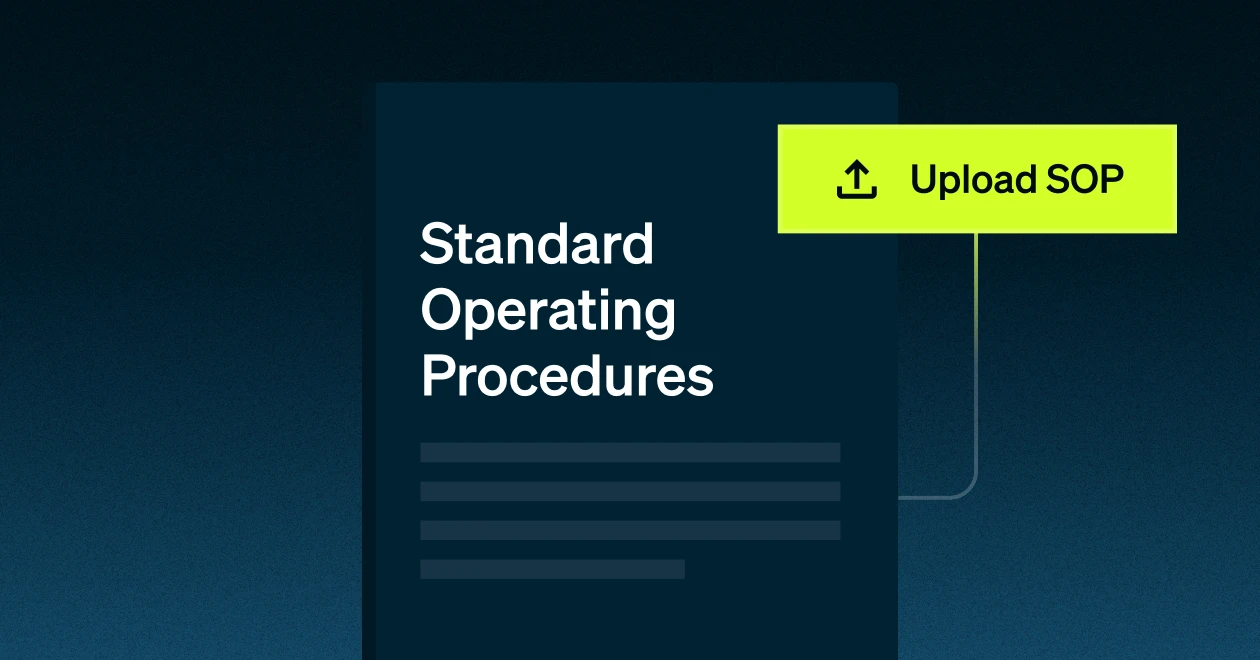
Overview
SOPs are an essential component of any security plan. They give your team a clear, concise set of guidelines so everyone knows their role and responsibilities, no matter how long they’ve been on the job. This starter packet includes customizable Standard Operating Procedure (SOP) templates for GSOC operators to follow during incident triage.
Benefits of SOPs:
- Expansion and scalability: Quickly enable your team at new locations, or onboard more employees
- Increased productivity: When everything is documented, there is no question as to what needs to be done
- Records against potential litigation: When there is a specific process to follow, which includes documentation, a company can use their SOPs as evidence of training and procedure
Posted on March 9, 2026 by Andrew - Uncategorized

How do you know if your security program is actually working? Most organizations can’t answer that question with data. This guide outlines four key considerations for measuring and proving security program effectiveness — from setting the right KPIs to building the business case for leadership. If your program has been running on gut instinct, this is your reset.
Posted on March 9, 2026 by Andrew - Featured, Uncategorized
The wrong tech stack doesn’t just waste budget — it creates noise, gaps, and operator frustration. This guide helps security leaders cut through vendor promises and build a stack that works. You’ll get the right questions to ask vendors, a framework for evaluating consolidation, and a clear path to technology that supports your security goals instead of complicating them.
Posted on March 9, 2026 by Andrew - Uncategorized

Security leaders are consistently asked to do more with less — and without a compelling budget proposal, it’s nearly impossible to get the investment your program actually needs. This guide walks through how to assess your current spend, build a proposal leadership will respond to, and communicate the real cost of doing nothing. Because underfunding security is always more expensive than the ask.
Posted on March 9, 2026 by Josh - Uncategorized

Your guards are the front line. But the relationship between security operations and field resources is often underdeveloped — and it shows. This guide covers how to build strong, collaborative relationships with guarding partners, the right questions to ask third-party providers, and how to use data to drive field performance. Because a strong GSOC is only as effective as the people it’s connected to.
Posted on May 4, 2023 by Andrew - Uncategorized
Overview
As the C-suite continues to prioritize ‘doing more, with less,’ physical security teams are often placed in the crosshairs. But tying their ability to protect against and mitigate risks to the financial impact on the company can go a long way in justifying additional investment in tools and technology that address physical security concerns.
This e-Book covers:
- What is a physical security breach?
- What is the cost of a breach (and some of the hidden costs that the company should consider)?
- How can companies address physical security risk through governance, culture, and technology?