The conversation around AI in physical security has shifted. A few years ago, it was all hype, pilot programs, and vendor promises. Today, enterprise security teams are deploying AI in production across access control, video surveillance, and incident management, and the gap between early adopters and everyone else is widening fast.
But for many security leaders, the question isn’t whether AI works. It’s where to start, what to realistically expect, and how to avoid the mistakes that derail implementation before it ever gets off the ground.
The state of AI in physical security today
AI in physical security is no longer experimental. Modern video analytics can distinguish between a person, a vehicle, and an animal with meaningful accuracy, which is a far cry from the motion-triggered false alarm machines that gave earlier-generation systems a bad reputation.
The market is also consolidating quickly. Major players in the security software space are embedding AI natively into their ecosystems, which means buyers increasingly get AI as a feature rather than a bolt-on product requiring yet another integration headache.
That said, integration remains the central challenge. The biggest barrier isn’t AI capability, it’s connecting modern AI tools to every physical security system in place at an organization. Legacy systems were never built with data interoperability in mind, which is necessary to make AI truly helpful.
And one thing hasn’t changed: human oversight remains essential. The best implementations today keep humans in the decision loop while AI handles volume and pattern recognition.
What does AI actually do well for physical security?
Across security programs, AI is delivering real, measurable value in four areas:
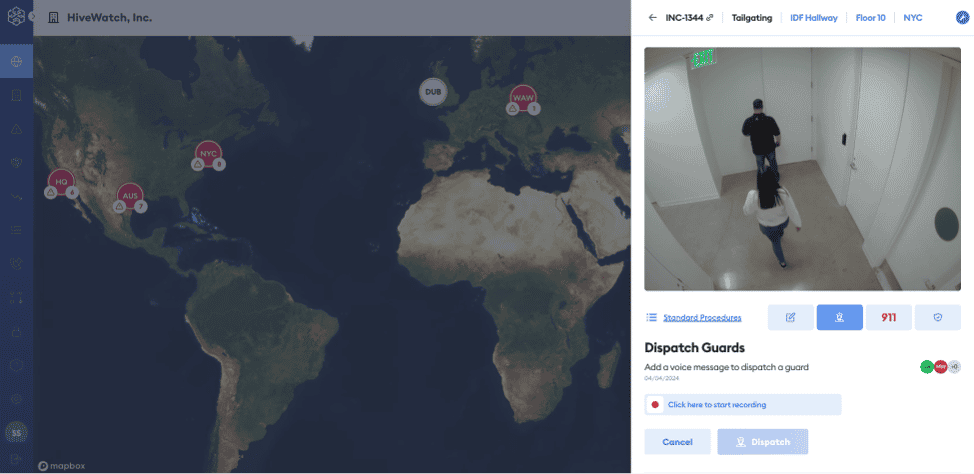
Automated alert triage is where most teams see the fastest ROI. AI filters false alarms from real threats, prioritizes by risk context, and dramatically reduces the manual review burden on analysts (often reducing it by 60 to 80%).
Intelligent video correlation moves beyond single-camera monitoring. Cross-camera object tracking, behavioral anomaly detection, and automatic event timeline reconstruction give investigators tools that used to require hours of manual footage review.
Predictive maintenance is underutilized but high-value. AI can offer details about device health in real time, predict failures before they cause coverage gaps, and help teams prioritize maintenance resources where they’re needed most.
Real-time device health monitoring gives security operations visibility into the status of every sensor, camera, and access point, with automatic alerts when devices go offline or degrade, at a scale no human team can match manually.
Where is the best place to start using AI?
The smartest security teams don’t try to automate everything at once. They start where the pain is loudest.
For most organizations, that’s alert fatigue and false alarm management. It’s the highest-friction, highest-ROI entry point, and it’s where AI can show measurable results quickly without requiring a full infrastructure overhaul.
From there, the approach is repeated for the next pain point. Deploy for one challenge at a time (or one piece of one challenge), measure rigorously, and report results transparently before expanding scope. AI’s role should expand as trust is earned (not as a condition of the initial business case).
A practical 90-day framework looks like this:
- Weeks 1-2: Audit alert volume and map pain points with operators and analysts.
- Weeks 3-4: Select one focused pain point to address, and identify a vendor with genuine physical security domain expertise.
- Weeks 5-10: Deploy with a limited number of operators to understand how it works, and establish what performance indicators should be before rolling out to the whole team.
- Weeks 11-12: Tune and optimize the system as operators and analysts use it, prepare and present results to leadership with a clear ROI statement.
What success with AI looks like
The top AI use in physical security isn’t just an operations story, it’s a business story.
Operationally, teams that implement AI well see analysts shift from reactive triage to proactive management. They see real incidents surface faster with less busywork to find them. And device uptime improve as failures become predictable rather than surprising.
The bottom-line impact is equally interesting and should be talked about. Lower cost-per-incident through automated responses, fewer emergency dispatch calls, reduced insurance premiums tied to improved risk controls, and operator reallocation from reactive work to strategic program management. These are board-reportable outcomes (MTTR, false alarm rate, system uptime) that translate security investment into business language.
The mistakes that derail it
Most AI implementations don’t fail in the technology. They fail in the execution. The most common pitfalls include trying to automate too much too fast, skipping change management with frontline operators, launching without a feedback loop to keep models calibrated, and underestimating integration complexity after a vendor promises plug-and-play simplicity.
The teams that win declare success on a narrow scope before expanding. Small wins generate the trust from leadership, from analysts, and from the organization that can fund and sustain the next phase.
That’s not a limitation of AI. That’s just good program management.
Ready to learn more about how to begin implementing AI in your security program? Let’s chat.