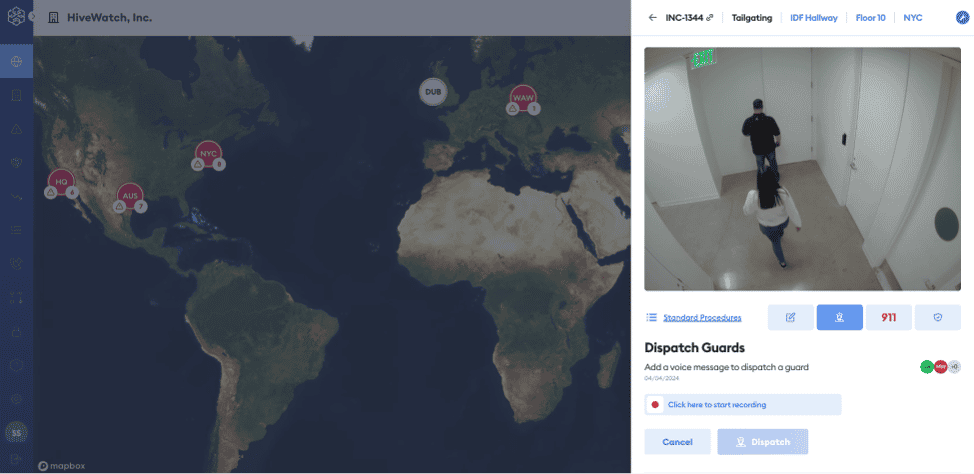
As threat landscapes become more sophisticated, there are very simple ways that bad actors might gain access to a facility. One often overlooked (but critical) security vulnerability is tailgating, also known as piggybacking.
Posted on January 24, 2025 by Haywood Hunter - Industry Expertise
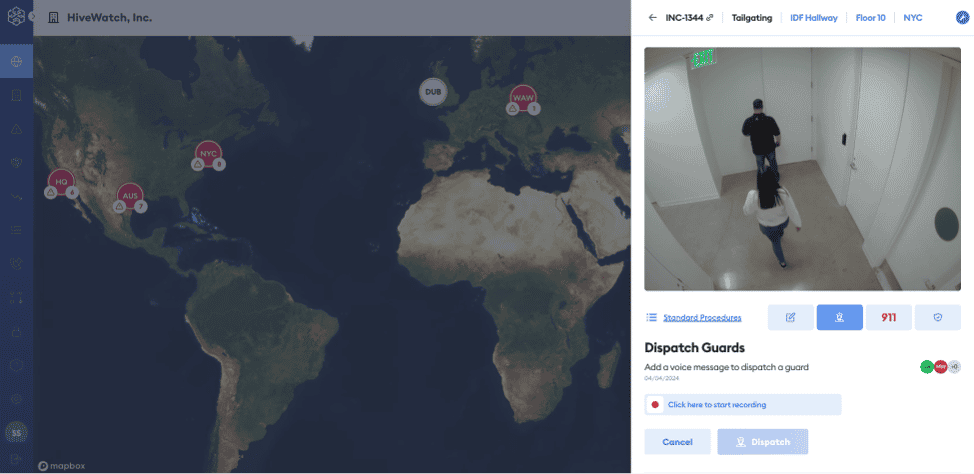
As threat landscapes become more sophisticated, there are very simple ways that bad actors might gain access to a facility. One often overlooked (but critical) security vulnerability is tailgating, also known as piggybacking.